Open Banking and Cyber Security in 10 Questions
1. What is Open Banking?
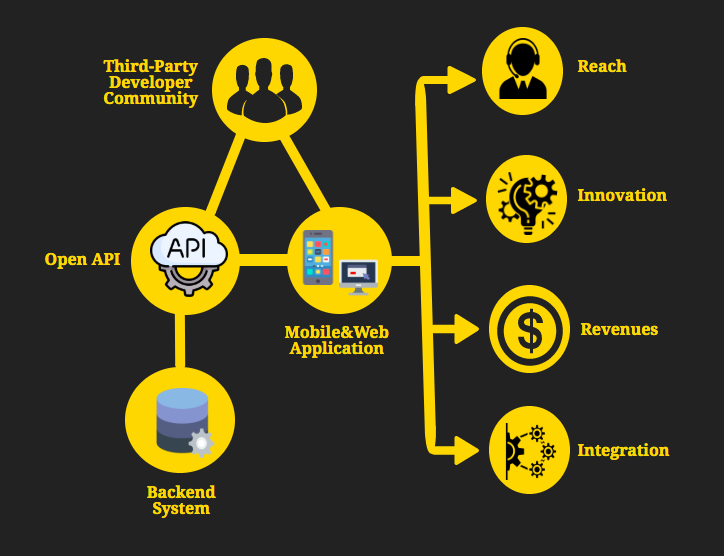
Open Banking is a system that shares financial institutions’ data, capabilities and/or processes to ensure the secure accession and availability of financial information to the users via third parties including fintech firms, technology providers, and other institutions by using Application Programming Interfaces (APIs).
Your financial information is yours, and if you want, you use open banking to make payments or share data. You do not have to participate in open banking and nothing is shared with services you have not signed up for.
Developments in Open Banking signals a transition that traditional banking will become a memory in the coming years. Open Banking continues to evolve worldwide and flourish despite difficulties.
There are pros and cons of Open Banking systems and you need to know more about to decide. Let’s get started.
2. What are Open-Banking APIs?
APIs are the key role in Open Banking initiatives. APIs are interfaces that allow banks to provide communications to Third Party Providers. These APIs are designed and documented to support PSD2 (see below) and Open Banking regulations.
3. What is PSD2?
PSD2 stands for the Payment Services Directive. With PSD1, which came into force in 2009 for the first time in EU countries, the main objective of the European Union was to develop an efficient, fast, standardized, secure, and competitive payment market among the union countries. PSD2 has emerged as a result of the 5-year review of every law in the European Union. PSD2, which was introduced in 2015, is an improved revision of the scope of PSD1.
Two different concepts have emerged with PSD2.
● Account Information Service Providers
● Payment Initiation Service Providers
These new definitions require access to the customer’s information in order to do their job, a procedure which requires further security. In PSD2, with the help of the APIs of the banks with the new security criteria, it is obligatory to share the information with third parties allowed by the customer.
4. What are the differences between Open Banking and PSD2?
Open Banking and PSD2 often seem to be used interchangeably but they are not the same. PSD2 is the regulation that allows projects such as Open Banking to take place. PSD2 tells businesses what new services and products they can offer, while Open Banking tells them how.
5. When it all started?
In October 2015, the European Parliament adopted a Payment Services Directive. In the U.K., regulators issued a ruling requiring the nine biggest banks to allow licensed startups direct access to their data and open banking has been a law since August 2016.
6. Which countries support open banking?
Open banking has crossed European borders and has started to develop in the following 8 countries besides EU countries:
● Australia: The Government commissioned a report that was made on the implementation of open banking.
● Canada: The Government has already budgeted for a report to evaluate how to introduce open banking in the country.
● Hong Kong: The monetary authority has recently published a report on open APIs.
● Japan: Government, the entry into force of the European PSD2 has served to boost the opening of the financial ecosystem in Japan.
● Israel: The Bank of Israel reflects in its recently published 2017 annual survey its commitment to “promote open banking through the publication of an API standard that will allow customers to transfer information and compare alternatives”.
● Mexico: The Chamber of Deputies approved the Fintech Law, in which cryptocurrencies and APIs.
● New Zealand: The financial ecosystem leads the open banking initiative through the industry association Payments NZ, working to launch two payment APIs.
● Singapore: The Monetary Authority of Singapore has chosen to encourage financial institutions to make use of APIs to drive innovation and interoperability
7. Are there major banks that support Open Banking?
Yes. For instance, the UK’s top nine banks are required to support open banking which included:
● Royal Bank of Scotland Group (Natwest, Ulster Bank, and Royal Bank of Scotland)
● Santander
● Barclays Bank
● HSBC Group (HSBC, First Direct, M&S)
● Lloyds Group (Lloyds, Halifax and Bank of Scotland)
● Nationwide
● Danske Bank
● Bank of Ireland (including the Post Office)
● Allied Irish Banks (including AIB and First Trust Bank)
Smaller banks (Starling Bank, Monzo, Metro Bank) are more open to change but face challenges about implementing the open banking APIs.
8. What are the consumers’ worries about Open Banking?
Ipsos’ research with 15,000 individuals in 15 countries provides an overview of what the mentioned fundamental changes mean to consumers.
According to the research, there are 5 main concerns:
● 57% of respondents are concerned about how personal financial data will be used.
● 54% are concerned that my personal financial data will be obtained by malicious parties
● 53% say I don’t feel confident sharing my personal financial data.
● 51% say I don’t know who holds my personal financial data
● 49% think there will be a lack of protection of personal data.
9. How secure is Open Banking?
Security is the most important when it comes to financial transactions. We choose really compelling passwords, even for the password of any bank card. this becomes even more important when it comes to open banking. All third-party providers have to comply with data protection rules, including GDPR regulation. The provider must tell you exactly what data to use, how long it will remain, and what to do before you sign up.
Security is an important issue for banks as well as consumers in open banking. Because open banking means that banks open their systems to authorized third-party financial service providers. Open APIs make banks dependent on the security of the third-party providers (TPPs) using these APIs.
Some threat scenarios include:
● A data breach at a TPP leak:
TPPs store a consumer’s financial data. If a TPP is breached, it may disclose the customer data of the bank and may affect the bank’s reputation. In addition, this breach affects all banks in which financial data is stored in TTP.
● Hacked at a TPP:
A TPP may be attacked due to security vulnerabilities in the TPP’s mobile app or web app. Such an attack could result in fake payment requests from the TPP to the bank.
● Untrusted TPP employees:
An untrusted employee in a TPP may make fake claims/initiate fraudulent payments to obtain information about a bank’s customers.
10. How banks can evaluate the security of third-party service providers?
Since banks are the first party held responsible for unauthorized financial transactions from a user’s bank account, a security breach in a TPP can have serious consequences for banks. Therefore, banks have to mitigate the risks posed by open banking by assessing the cyber risk of TPPs.
Security control is a far-reaching topic and it is important to look at important details, from the awareness of its employees to the versions of the services the company uses. It is also necessary to monitor compliance with regulations and to make risk assessments of its impact on the bank in case of a possible attack.
Black Kite helps organizations to give a multidimensional risk view of their vendor by providing risk analysis in terms of technical findings, compliance, and financial risk.
● Black Kite Cyber Risk Scorecards (technical): The Scorecard provides easy-to-understand risk scores for a company and the ecosystem formed by its third parties. Black Kite produces technical findings for cyber risk management at 20 categories, 500+ security checkpoints, with non-intrusive external scanning using only the domain name.
● Shared Assessments’ SIG Questionnaire (policies and processes): Banks should monitor and assess the cyber risk of their third parties and understand the level of GDPR compliance required of a third-party vendor. A vendor may be more familiar with other regulations, such as PCI-DSS, NIST 800-53, etc. rather than GDPR. For instance, a vendor that deals with credit card transactions may be more familiar with PCS-DSS. Fortunately, Black Kite offers cross-walking between regulations and frameworks, making the task of tracking and meeting requirements. Black Kite can also correlate information provided by third parties to their customers (the outsourcers) on other regulations, such as NIST 800-53, PCI-DSS, ISO 27001, COBIT, and GDPR.
● FAIR analysis (the probable impact in financial numbers): Using the FAIR Model, Black Kite enables organizations to calculate the potential financial impact of cyber attacks on suppliers and partners.
Request a free scorecard and a free FAIR report to see how Black Kite assesses the cyber risk of a company.