By 2020, More Than 3,500 New Phishing Domains will be Active, Targeting 50 Major Banks
The European Central Bank (ECB) website was hacked in August by an unknown group in the hope of being able to conduct phishing attacks. The hack has been utilized for phishing exercises, whereby adversaries attempt to acquire sensitive data or cash through misdirection.
The financial industry is one of the top targets of hackers using phishing attacks. Most of the time, the first step of a successful scam is a phishing attack. Phishing consists of several steps to ensure credibility. Hackers don’t shy away from these steps because they can easily win in the end and as in ECB, they can target the server where they can obtain more information about the customers connected to the bank.
Our recent research revealed that phishing domains are on the rise for the banking industry. We investigated phishing domains impersonating 50 major banks in the world and the results were shocking.
Why Do Attackers Use Phishing Attacks?
Phishing attacks always start with a scheme to trick consumers into thinking they are doing business with a company or organization that they already trust. Hackers create websites to impersonate financial institutions and to get consumers to reveal sensitive information such as credit card and banking information.
While countermeasures are taken for both internal network, external banking websites and apps safety, it is frequently the human component that neglects to identify the scam that causes a data breach.
The Impact of Phishing Attacks
- Phishing is the number one cause of data breaches.
- Name-blending phishing domains are exploited not only to steal credentials, but also to help attackers cover their tracks.
- Phishing targets bank employees and customers. Even though companies cannot be directly held responsible for customers’ being deceived by phishing scams, the bank still takes a significant hit to brand reputation and customer trust.
Phishing attacks are extremely costly for both consumers and banks, robbing consumers, putting them at risk of further losses and greatly damaging trust and brand reputation for banks.
Black Kite investigated 50 major global financial institutions. Black Kite’s The State of Financial Phishing Report reveals 1,900+ potential phishing domains were registered in the first half of 2019 alone.
1,900+ Phishing Domains Registered in 2019-H1 Alone
Although cybercrime covers a wide range of online offenses, it is phishing that is a primary concern for financial institutions. There was a 14% increase in the number of phishing domains registered in the first half of 2019 compared to those registered in the same period in 2018.
- Slow start-rapid increase : In 2019, potential phishing domains started to appear very slowly, but rapidly increased after March.
- 3,500 new domains expected: By year’s end, more than 3,500 new phishing domains will be active.
- Attacks in waiting: Hackers like to wait for the right moment. Some domains that were registered last year, but not used, are still at risk for activation.
The Padlock Icon May be Decisive
The padlock icon displayed in the browser address bar (https at the URL) indicates a domain has a valid SSL or TLS certificate and indicates a certain level of security. However, 15% of potential phishing domains registered in the first half of 2019 were able to impersonate a valid bank certificate.
The number of certified phishing domains increased more than 2X as compared to 2018-H1. Every year, hackers improve their techniques and become more intelligent. It is no surprise to see the increase in the number of phishing domains with valid certificates.
European Banks Are More Targeted For Phishing Attacks
The number of potential phishing domains for European banks among the 50 major banks studied is higher than the ones in other regions.
How To Identify a Phishing Domain
They all included standard email or website interchanges that upon first look appeared to be authentic. They had official-looking logos and email addresses or were customized somehow or another.
Understand if a website is a phishing website by checking the following:
- Whether the URL is typo-squatted or not
- The date of registration
- Page rank
- Domain provider
- SSL certificate provider
Get better ideas here:
Are There Any Domains Impersonating Your Company For Phishing?
How To Search For Phishing Domain Targeting Your Organization
Black Kite’s Free ‘Potential Phishing Domain Search‘ is used to investigate phishing domains impersonating banks.
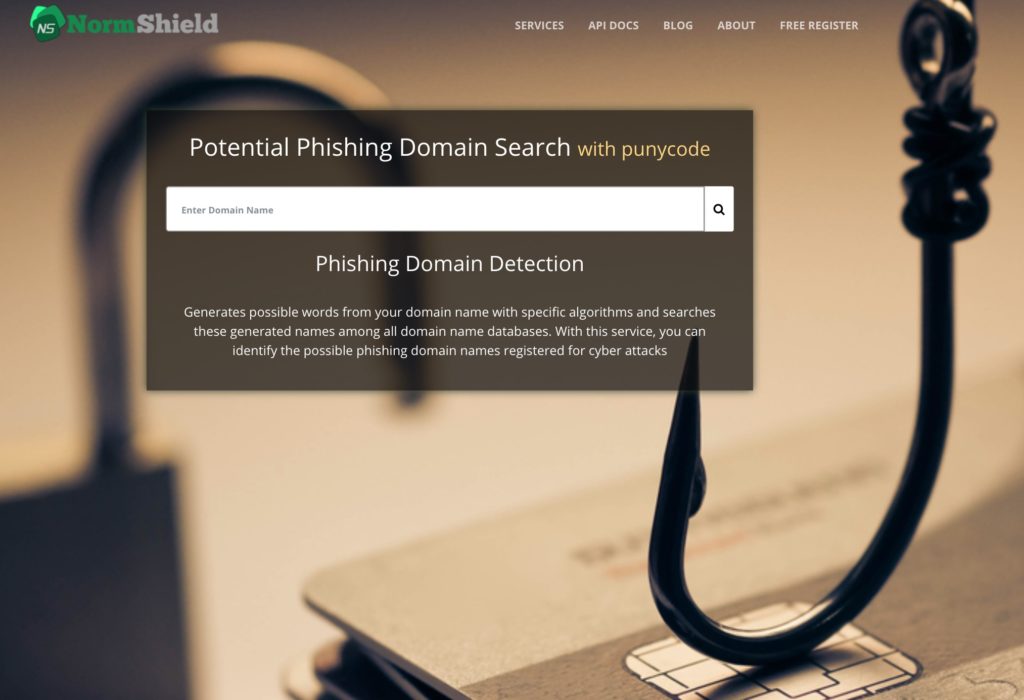
Black Kite’s Phishing Domain Search generates word combinations for the given domain name with specific algorithms and searches these generated names among all the domain name databases. With this service, you can identify potential phishing domain names registered for cyber attacks. Using this powerful tool is quite easy. Enter the domain name and hit enter or click on the search button. Evaluate your organization’s defenselessness to phishing assaults and see who takes the draw.
Phishing domains pose a significant cyber risk for major banks. Learn how many phishing domains for major banks exist and how to find them in our “The State of Financial Phishing Report.” Knowing the risks to your business gives you the confidence to make successful decisions and protect yourself.

